TodayMicrosoft released a set of fixes for Remote Desktop Services that include twocritical Remote Code Execution (RCE) vulnerabilities, CVE-2019-1181 and CVE-2019-1182. Likethe previously-fixed ‘BlueKeep’ vulnerability (CVE-2019-0708), these two vulnerabilities are also ‘wormable’, meaning that anyfuture malware that exploits these could propagate from vulnerable computer tovulnerable computer without user interaction.
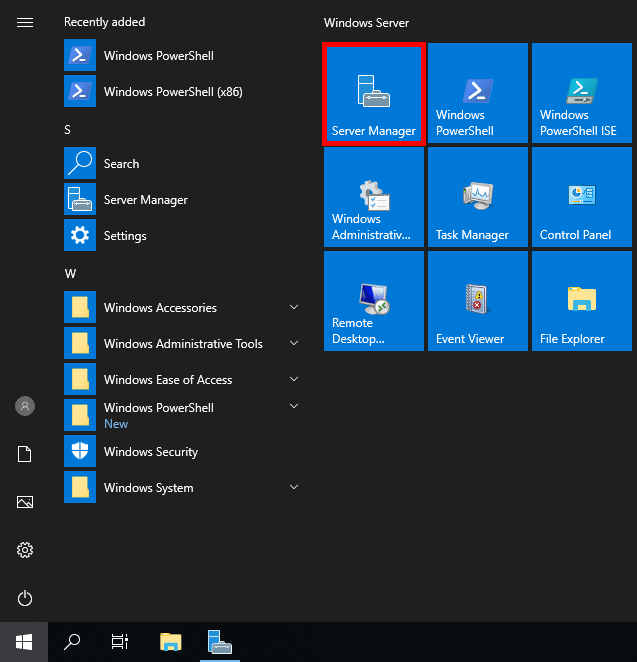
Add the secondary server by right-clicking on the All Servers, choosing Add Servers, and then picking the server from Active Directory. Navigate to Remote Desktop Services and click on the green plus for RD Licensing. Remote Desktop Services - Multi-Factor Authentication.; 2 minutes to read; l; e; D; H; M; In this article. Applies to: Windows Server (Semi-Annual Channel), Windows Server 2019, Windows Server 2016. Leverage the power of Active Directory with Multi-Factor Authentication to enforce high security protection of your business resources.
The affected versions of Windows are Windows 7 SP1, Windows Server 2008 R2 SP1, Windows Server 2012, Windows 8.1, Windows Server 2012 R2, and all supported versions of Windows 10, including server versions.


Windows XP, Windows Server 2003, and Windows Server 2008 are not affected, nor isthe Remote Desktop Protocol (RDP) itself affected.
These vulnerabilitieswere discovered by Microsoft during hardening of Remote Desktop Services aspart of our continual focus on strengthening the security of our products. Atthis time, we have no evidence that these vulnerabilities were known to anythird party.

It is important that affected systems are patched as quickly as possible because of the elevated risks associated with wormable vulnerabilities like these, and downloads for these can be found in the Microsoft Security Update Guide. Customers who have automatic updates enabled are automatically protected by these fixes. By default, Windows 10 Home and Windows 10 Pro users will be updated automatically.
Thereis partial mitigation on affected systems that have Network LevelAuthentication (NLA) enabled. The affected systems are mitigated against‘wormable’ malware or advanced malware threats that could exploit thevulnerability, as NLA requires authentication before the vulnerability can betriggered. However, affected systems are still vulnerable to Remote CodeExecution (RCE) exploitation if the attacker has valid credentials that can beused to successfully authenticate.
Resources
Links to downloads
How To Deploy Remote Desktop Services (RDS) 2019
SimonPope, Director of Incident Response, Microsoft Security Response Center (MSRC)




